Need fine-grained access control of your backups? Admins can now restrict access to CloudAlly Backup based on the users’ IP addresses. This is especially helpful to enforce security policies and prevent unauthorized access by limiting backup and restore requests to company-approved IP addresses, such as an office IP, or a particular VPN.
Setting Up IP Restrictions
To enable IP restrictions in your CloudAlly account, first create the list of trusted IP addresses.
IMPORTANT! It is strongly recommended to use this feature only if you have a static IP address, to prevent users from being locked out.
- In the Settings panel, click Security, and then IP Restrictions.
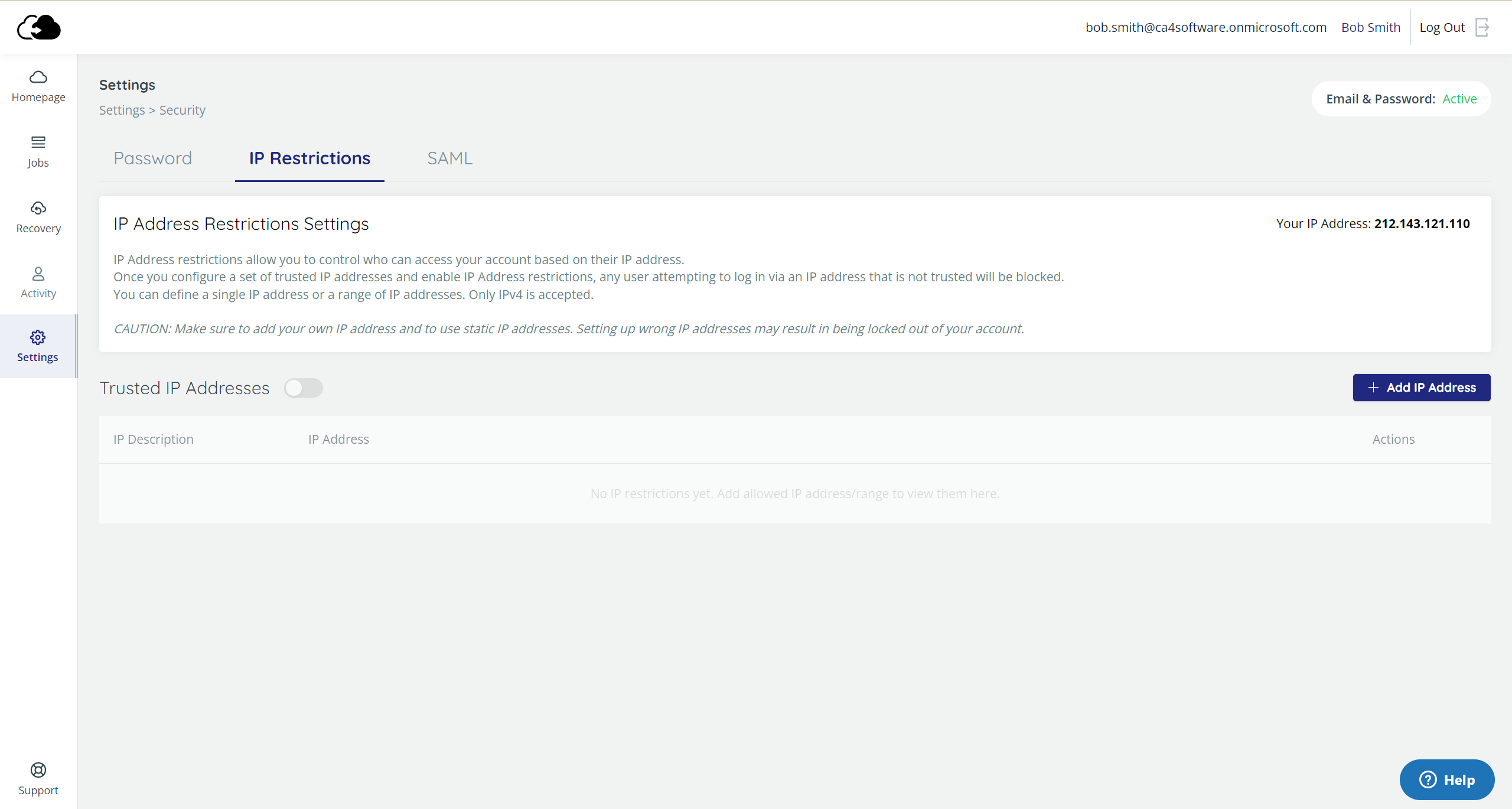
2. Click + Add IP Address.
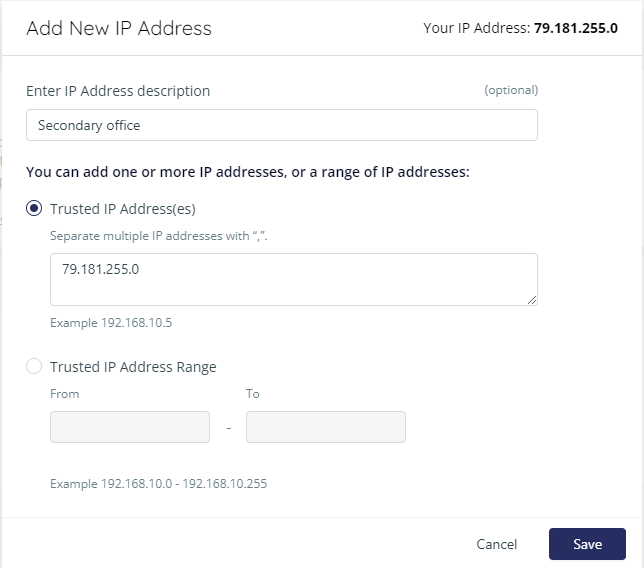
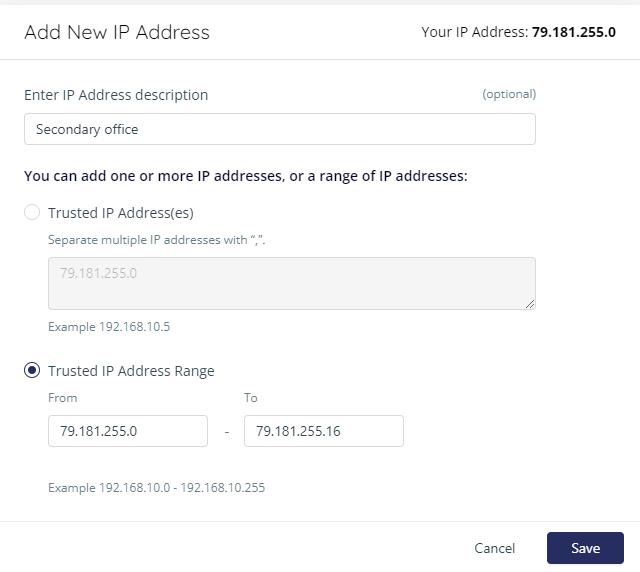
3. Enter one or more IP addresses:
- Enter individual addresses separated by commas, and an optional description.
- Or, enter a range of contiguous addresses, and an optional description.
4. Once you enter at least one address, the Trusted IP Addresses toggle will be turned on. You can always return to disable IP restrictions later on.
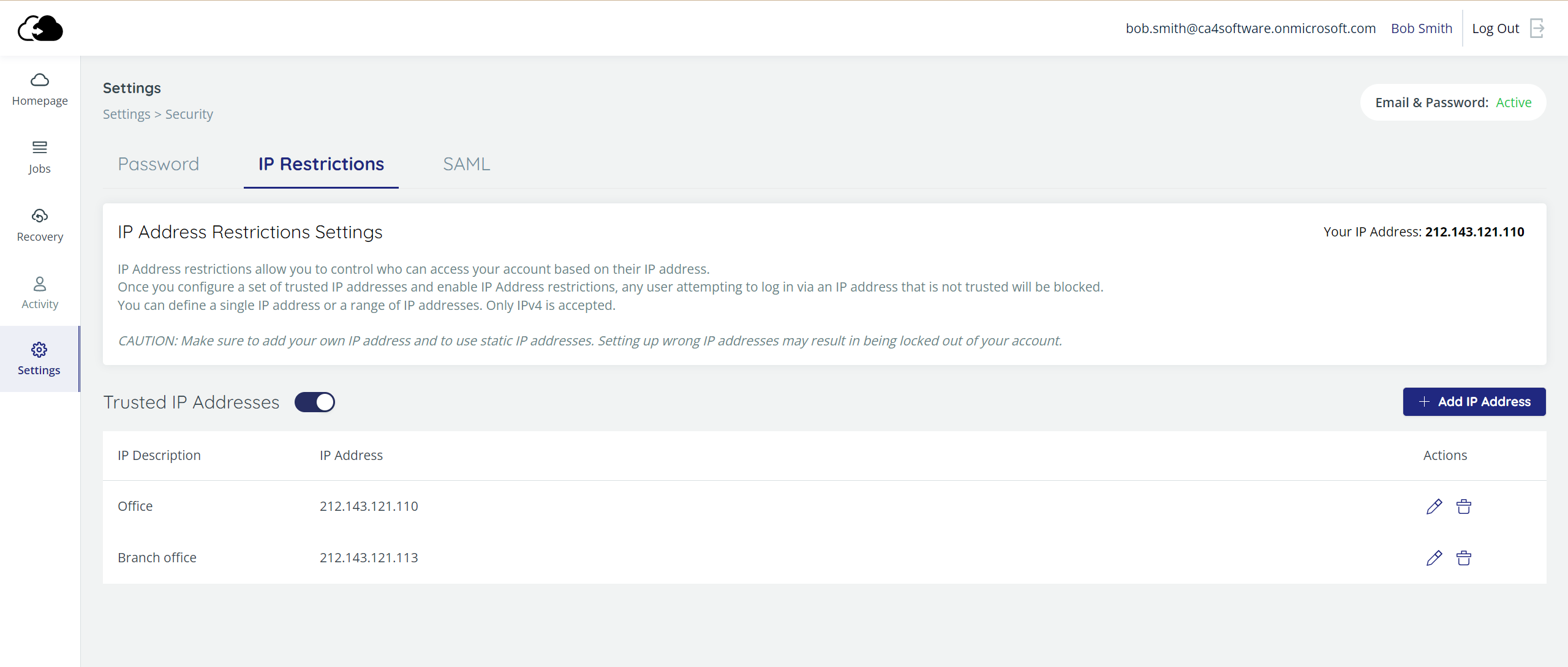
You can edit your list of addresses by clicking ![]() , or delete ones that you no longer want on your trusted list by clicking
, or delete ones that you no longer want on your trusted list by clicking ![]() .
.
NOTE: If you forget to include your own IP address on the trusted list, IP restrictions cannot be enabled.
Your CloudAlly account is now protected from access from IP addresses which are not on your list.
Blocking Access
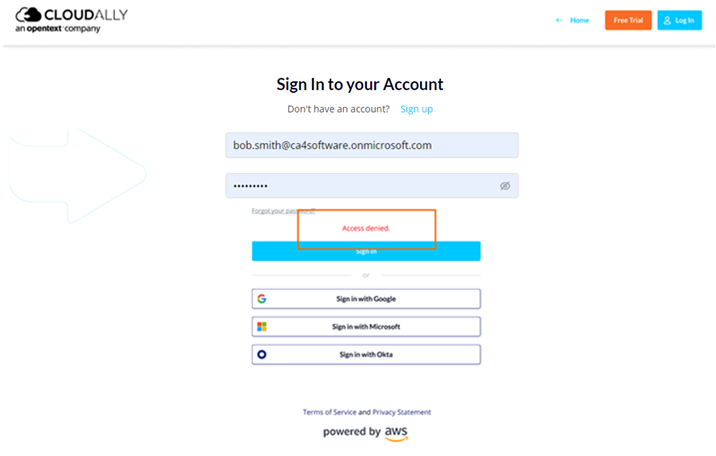
If a user tries to access your CloudAlly account from an untrusted IP address, the following “Access Denied” error message will appear:
Email Notifications
Whenever you enable or disable IP restrictions, or modify the addresses, CloudAlly will send you an email notification, letting you know what has changed.